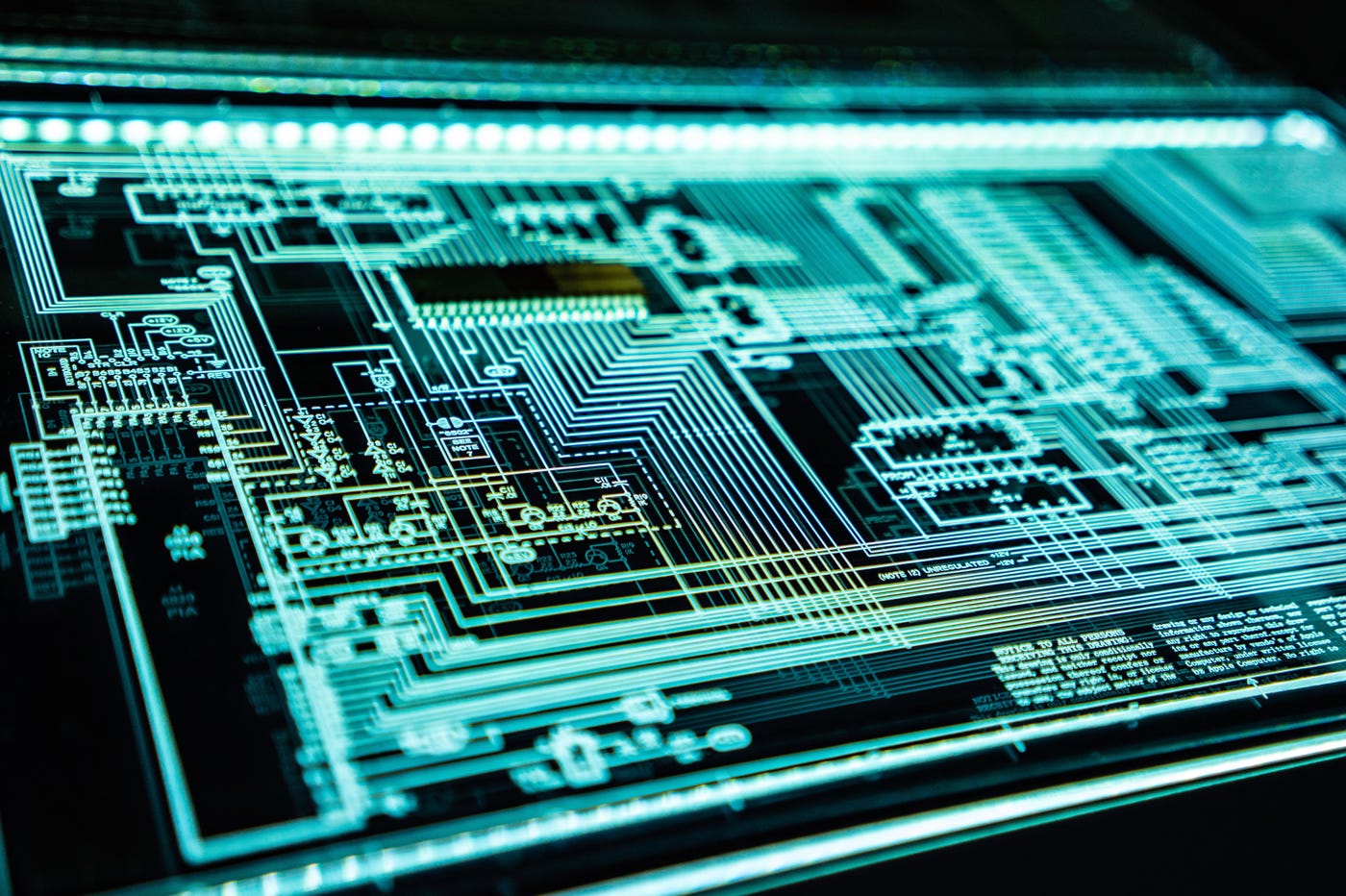
Researchers specializing in computer security revealed that they discovered a Apple silicon engineering flaw, which they called “Augury”. This can make it possible to collect information from a Mac equipped with a chip from the M1 family.
However, IT teams want to be reassured. The breach in question relates to the so-called “DMP” system, which can only refer to “sleep” data, i.e. data that no instructions (applications, programs, services, etc.) Also, it has been pointed out that only the most experienced hackers can take advantage of the opening that Apple engineers left there.
In short, this means that even if the Californian company takes some time to resolve this flaw, you won’t be risking much with your Apple silicon Mac computer.
Let’s take this opportunity to remind you Some best practices In terms of computer security, whether you use a Windows computer, a Mac computer with an Intel processor, or a Mac computer with an Apple processor on a daily basis:
- Never open an attachment in an email from a sender you don’t know
- Ditto for an attachment received on your iPhone or iPad elsewhere, via email, iMessage, or another messaging service
- When paying online, always make sure that the little padlock appears in the address and that the URL begins with “https” and not “http”
- Try to download your apps and software only from the Apple App Store and official developer sites
- Use different passwords for each of your accounts. Apple’s password manager, Keychain Access, can help with this. But there are alternatives, see especially here
- Scan your Mac periodically for malware, using security suites like CleanMyMac where Antigo
find here The research paper signed by the team of academics on the Oguri error.
Read also:
Written by: Keleops AG

“Certified gamer. Problem solver. Internet enthusiast. Twitter scholar. Infuriatingly humble alcohol geek. Tv guru.”