CERT-AgID, i.e. Computer Emergency Response Team The agency Digital Italy, which reports directly to the Presidency of the Council of Ministers on digital security issues, has launched a Specific alarm it’s a A new computer virus It only affects hardware Male in appearance. This is the Malware Flu bot It is very dangerous for affected devices, as well as having a large ability to self-copy immediately after entering a smartphone or tablet.
Like many other viruses that have been circulating since the Covid-19 pandemic it has caused it to boom Online shopping, Which leads to dozens of parcels and packages being delivered to the home every month, even this dangerous symbol takes advantage of a famous name Express Mail It tricks the user into telling them the existence of a file The parcel is waiting. The virus is transmitted through short messageTo be precise, it’s a campaign Fraud. Here’s how to recognize the dangerous message.
Flobot Virus: Dangerous Text Messaging
The main method for spreading the Flu Bot virus is an SMS message sent to a user’s SIM card. In the message, in correct Italian, you are talking about a non-existent parcel waiting to be opened by downloading the tracking app DHL courier. There are many variants of this SMS and some of them refer to other telecommunications companies, but in principle they are all the same:We have your package waiting“,”Your package is on its way“,”Package waiting [numero di telefono] Please check details and confirm“,”Tomorrow we will deliver your package“.
However, every SMS sent contains the same LinkThis prompts the user to download the file DHL.apk (Or similar, if another courier is copied) from which the actual infection starts.
How Flu Bot works and why is it dangerous
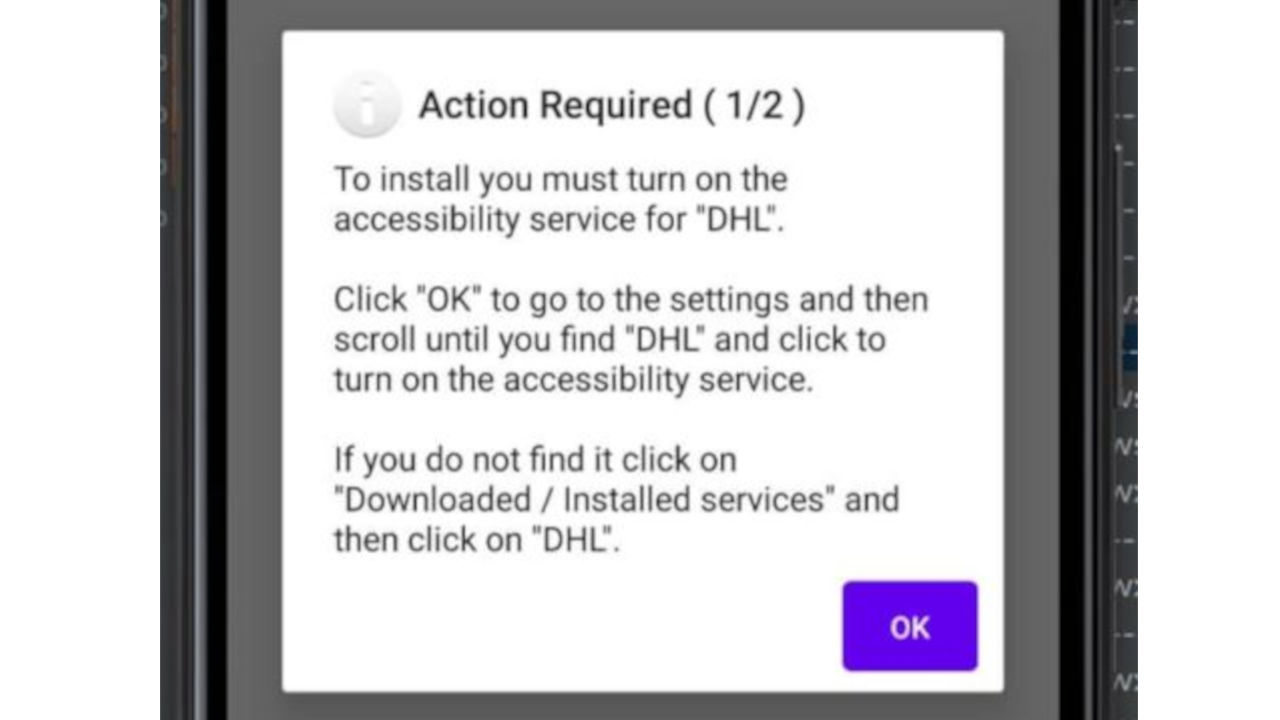
When the recipient of the message clicks on the link and downloads a file Infected apk file It’s already too late: link leads to Phishing page Which faithfully and honestly duplicates the look of the official DHL website. While the user views this page, the infected site starts a file Download in the background From DHL fake tracking app. At the end of the download, the application installation begins, which asks the user to access something called “Access permissionsFor Android OS.
These permissions are designed to allow certain actions for apps that facilitate listening and reading for the visually impaired and the visually impaired, but in the case of this affected app, they are used for a completely different purpose: onscreen display Fake Shermate Every time the user tries to access a site it requires logging in with a username and password.
The Flu Bot virus mimics login pages for social networks such as The social networking site FacebookChat apps like The WhatsApp, And email boxes like Gmail Above all, from Online banks. The fake screen is a mask created to collect login data and then send it to Control Server On Flow Bot.
But not only that, because Flow Bot also shows one Google Play Protect screen is fake (A legitimate Google service built into the Android operating system) through which it asks the user to enter all their data credit cards.
Among the various permissions that the affected app requires, there is also a license for Access to the directory From the device, which also allows the virus to steal our contacts’ phone numbers, which will then be used Send other dangerous text messages In order to further spread the infection.
For this reason, one way to check if your device is infected with Flu Bot is to verify List outgoing SMS: If we find a lot, but we haven’t sent it, it is very likely that the dangerous messages left our smartphone without our knowledge. In this case, after removing Flu Bot from our devices, it would be a good idea to contact all recipients of these SMS messages to let them know what happened.
With always access to SMS, Flu Bot can also read messages sent from banks like The second authentication factor Of transactions, allowing hackers to remotely control the virus Make bank transfers From victims’ checking accounts to foreign accounts they control.
Again for the same purpose it can compose the Flu Bot as well USSD trigger codesThat is, those for activating phone functions such as Call forwarding. Technically speaking, then, Flo Bot is …infostealer“Extremely powerful and dangerous.
How to remove flobot virus
As always, when it comes to computer viruses, the best remedy is block: You shouldn’t Do not click or tap On any link received via email, SMS or WhatsApp message if you are no longer sure it is a safe link. Not to mention giving out your sensitive data (and credit card and bank account data are more sensitive than others) to any website or app for no apparent reason.
If we are making a purchase online and we are asked to enter credit card details, in fact, we can obviously enter it using Reasonable certainty This data is safe. But if an app asks us to enter data without a good reason, then sure enough something is wrong as well.
Fortunately, there is a good and safe way to Flo Bot removed Even after the injury: The security researcher Linuxct He actually created a special tool. It is an application that you can download to your smartphone and start removing malware with complete independence. The Linuxct tool is available at this is the address.
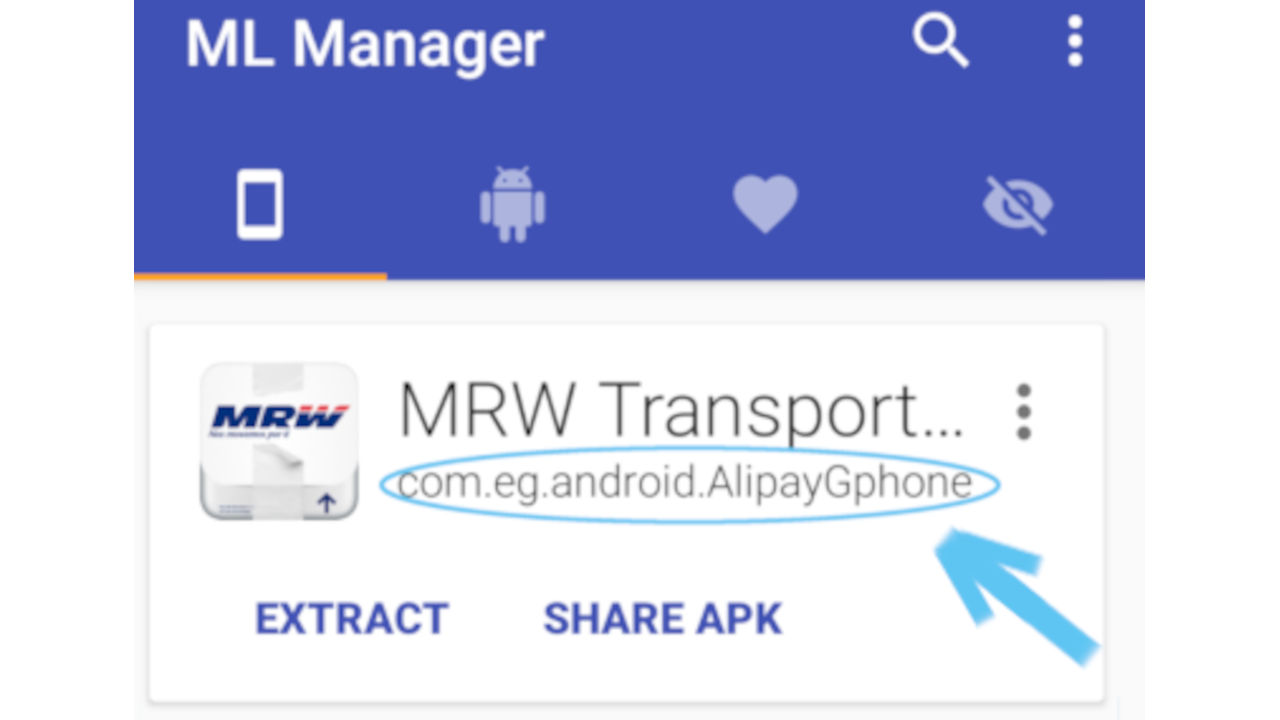
To use the Linuxct tool, you must first download the application ML Director Dal Play Store a this is the address. It is a safe app to manage apk files. After installing ML Manager, you need to open it and search for the application from which you started the Flu Bot infection, which will most likely have a name that looks like a courier like FedexAnd the DHLAnd the MRW Or similar. If we find with ML Manager two or more Chrome app It’s very likely that Flu Bot entered your Android device from one of them and not through a fake messenger app.
Once you have found and identified the affected application within ML Manager, you will need to take a note of Name of the installation package Which appears under the name of the application. It will probably look likecom.tencent.mm“Oh”com.eg.android.AlipayGphone“.
At this point, depending on the package name of the affected application, you need to click on one of the following links:
The application required to remove the Flu Bot virus will be downloaded and installed from your device. At the end of the procedure, it will be possible to uninstall both ML Manager and the later downloaded application by going to Settings> Applications and notifications> App info Then search for the respective applications and select them uninstall.
As an alternative to this procedure, which is effective but not very simple, there is a simpler but drastic option: Proceed to Full device reset For factory settings. This will erase all our data from the smartphone, as well as the infected app and Flu Bot virus files.
To reset a smartphone, you have to go to Settings> System> Reset Options> Wipe All Data (Factory Reset).

“Web fanatic. Travel scholar. Certified music evangelist. Coffee expert. Unapologetic internet guru. Beer nerd.”